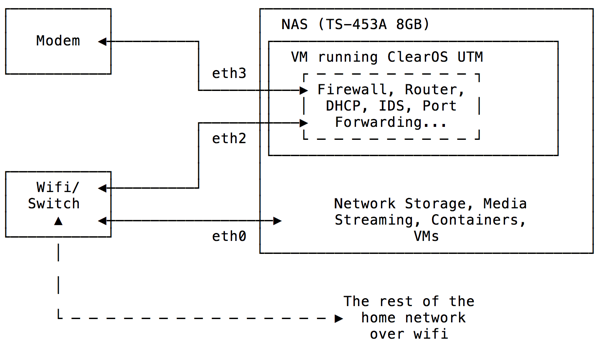
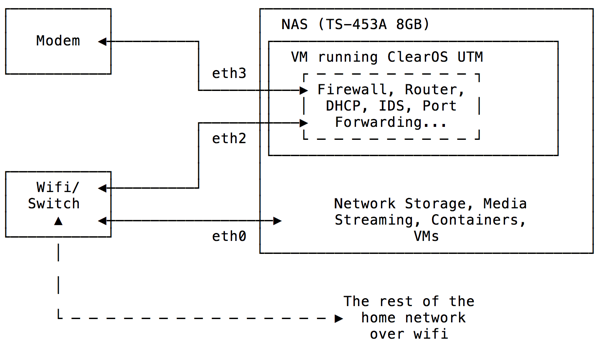
shazoom wrote:If anybody else is considering running a UTM on their NAS I can share my experience a week in.
No offense taken and my apologies if I were brash myself. If you're itching for misunderstandings, this is the place to be.

So...speaking to my pfSense VM (and never mind the Win Server) it runs much more smoother and efficient than Sophos as far as RAM and CPU usage are concerned.
And this is with many of the bells and whistles:
- WAN as PPPoE (set ISP modem as bridged)
OpenVPN client (with killswitch)
OpenVPN server
snort (both WAN and (passive) LAN prevention/detection)
pfBlockerNG (with 12 IP, 7 DNS block lists (around 700,000 blocks)
DHCP
NTP
darkstat
ntopng
etc
DNS is handled by Windows Server with pfSense as the forward.
Understand that unlike Sophos, pfSense allows extremely granular tweaking when it comes to how much
memory and
processing power you give
each item.
In other words all lists, features and add ons. Buffer sizers, caches, thresholds, priorities...perfect for all types of systems.
pfsense1.PNG
pfsense2.PNG
The latter pic is while the Windows Server is running as well.
That being said, I've done away with squid (and all caches). Too many issues, too much slow down and across all the platforms that I've used it, it doesn't always play nice so things break.
Your best bet is to use the one included with QTS as it will (hopefully) work independent of the router...though I think it will still break things.
I find no use for them except for maybe the inline virus scanning. I used to need it for adblock, but now pfBlockerNG is able to do that.
Here is the mem/proc usage (including the OpenVPN):
pfsense3.PNG
I've had the NAS hang on beta. Upon restarting there was an issue with port 4 (pfSense WAN, isolated net) where the static IP reverted to factory default.
Shutting down the VMs and restart again fixed it.
I have restarted the NAS on occasion while the VMs were left running. I have found no evidence of corruption. However, looking at pfSense you can see that it does work on it's system clock
when the NAS comes back on. Leaving it as such seems to be ok (though I restart the VM due to mild OCD). The Windows Server does the same thing and loses time. I've had to create a custom
time schedule to have the time feature sync constantly every 15 mins on it.
As far as the virtual switch thing, I am not sure.
What I have done is set all of them to static on the NAS, MTU 9000, pfSense as gateway and DNS server as Windows Server IP (or PIA VPN servers if not joined to domain).
It 'hiccups' on startup (before Virtualization Station) and complains about DNS/DHCP services, but smoothes over once pfSense VM comes back on.