And: is it affecting QTS NAS only, or are other QNAP products being hacked too?
[RANSOMWARE] >>READ 1st Post<< Deadbolt
- OneCD
- Guru
- Posts: 12144
- Joined: Sun Aug 21, 2016 10:48 am
- Location: "... there, behind that sofa!"
Re: [RANSOMWARE] Deadbolt
Knowing the firmware versions of affected units would be helpful. 
And: is it affecting QTS NAS only, or are other QNAP products being hacked too?
And: is it affecting QTS NAS only, or are other QNAP products being hacked too?
- jaysona
- Been there, done that
- Posts: 854
- Joined: Tue Dec 02, 2008 11:26 am
- Location: Somewhere in the Great White North
Re: [RANSOMWARE] Deadbolt
Woah, woah there. Let's keep some level of intellectual honesty here. There is no indication that these perpetrators are terrorist, they are most assuredly criminals.
The blame for this lies squarely on QNAP though. QNAP has repeatedly been exploited for more than six years now, and repeatedly by the same types of attack vector. Yet, during the past six years QNAP has done little to actually deal with and address the problem of the extremely poor coding practices (hard coded credentials in 2021? Seriously, wtf?) employed in the QTS operating environment and all the various "Q" applications.
QNAP has utterly decimated the basic security model of Linux and makes it all but impossible for any user to employ any of the basic security functions that are part of Linux. 3rd party application developers such as Plex have made requests to QNAP several years ago asking QNAP to at least make it possible for applications to run in their own user space and not be required run as Admin, for example. QNAP essentially told 3rd party application developers that were asking for better security models to take a long walk off of a short pier.
Instead, QNAP continued to muddy the already very muddy security waters by releasing QuFirewall and giving the impression that using QuFirewall made the NAS secure and could be made accessible from the Internet. Further muddying of the waters continued with never ending messaging and push to use Security Counselor, Maleware Remover, QVPN, automatic updates, etc. None of these action actually dealt with impeding attacks such as this and previous ransomware attacks.
QNAP has done absolutely nothing to impede the exploitation of these types of security vulnerabilities and has set-up their technology-illeterate and security-illiterate user base to be exploited by the plethora of security vulnerabilities that are present in the QTS operating environment and the "Q" applications.
With the release of the TS-509 Pro and all subsequent Intel x86 & x86_64 based NASes, there was no reason to keep QTS based on a crippled low powered embedded Linux type of build. The Linux build on home routers in many cases, are more robust and secure than the Linux build that QTS is based on.
At this point? That is something that QNAP should have been actively advocating as far back as 2015.Disable port-forwards and UPnP should be considered a bare minimum at this point.
RAID is not a Back-up!
H/W: QNAP TVS-871 (i7-4790. 16GB) (Plex server) / TVS-EC1080 (32Gig ECC) - VM host & seedbox
H/W: Asustor AS6604T (8GB) / Asustor AS7010T (16GB) (media storage)
H/W: TS-219 Pro / TS-509 Pro
O/S: Slackware 14.2 / MS Windows 7-64 (x5)
Router1: Asus RT-AC86U - Asuswrt-Merlin - 386.7_2
Router2: Asus RT-AC68U - Asuswrt-Merlin - 386.7_2
Router3: Linksys WRT1900AC - DD-WRT v3.0-r46816 std
Router4: Asus RT-AC66U - FreshTomato v2021.10.15
Misc: Popcorn Hour A-110/WN-100, Pinnacle Show Center 250HD, Roku SoundBridge Radio (all retired)
Ditched QNAP units: TS-269 Pro / TS-253 Pro (8GB) / TS-509 Pro / TS-569 Pro / TS-853 Pro (8GB)
TS-670 Pro x2 (i7-3770s 16GB) / TS-870 Pro (i7-3770 16GB) / TVS-871 (i7-4790s 16GB)
H/W: QNAP TVS-871 (i7-4790. 16GB) (Plex server) / TVS-EC1080 (32Gig ECC) - VM host & seedbox
H/W: Asustor AS6604T (8GB) / Asustor AS7010T (16GB) (media storage)
H/W: TS-219 Pro / TS-509 Pro
O/S: Slackware 14.2 / MS Windows 7-64 (x5)
Router1: Asus RT-AC86U - Asuswrt-Merlin - 386.7_2
Router2: Asus RT-AC68U - Asuswrt-Merlin - 386.7_2
Router3: Linksys WRT1900AC - DD-WRT v3.0-r46816 std
Router4: Asus RT-AC66U - FreshTomato v2021.10.15
Misc: Popcorn Hour A-110/WN-100, Pinnacle Show Center 250HD, Roku SoundBridge Radio (all retired)
Ditched QNAP units: TS-269 Pro / TS-253 Pro (8GB) / TS-509 Pro / TS-569 Pro / TS-853 Pro (8GB)
TS-670 Pro x2 (i7-3770s 16GB) / TS-870 Pro (i7-3770 16GB) / TVS-871 (i7-4790s 16GB)
- Cbrad01
- Know my way around
- Posts: 245
- Joined: Fri Jan 15, 2016 9:17 pm
Re: [RANSOMWARE] Deadbolt
People need to stop exposing their NASs to the internet and QNAP needs to ditch the current os and all of the crap applications that create so many holes by trying to be the easy, no fuse internet cloud.
Google, Apple, Amazon and so spend billions on their cloud options to keep them secure and rebuts yet QNAP marketing let’s folks think they can do the same for a few hundred bucks and this is where we are.
QNAP has created a insecure OS with their decisions over time to make things easy and then putting crappy apps on top that all run privileged because it’s easy.
But with that said I am surprised that anyone thinks it’s safe to share their devices on the internet(regardless of what device it is).
Unless you are prepared to spend the time and resources to protect yourself leave cloud sharing to the big boys and use their services. Use your NAS inside your network to to share…
Sent from my iPad using Tapatalk
Google, Apple, Amazon and so spend billions on their cloud options to keep them secure and rebuts yet QNAP marketing let’s folks think they can do the same for a few hundred bucks and this is where we are.
QNAP has created a insecure OS with their decisions over time to make things easy and then putting crappy apps on top that all run privileged because it’s easy.
But with that said I am surprised that anyone thinks it’s safe to share their devices on the internet(regardless of what device it is).
Unless you are prepared to spend the time and resources to protect yourself leave cloud sharing to the big boys and use their services. Use your NAS inside your network to to share…
Sent from my iPad using Tapatalk
- OneCD
- Guru
- Posts: 12144
- Joined: Sun Aug 21, 2016 10:48 am
- Location: "... there, behind that sofa!"
Re: [RANSOMWARE] Deadbolt
Finally made the news: https://www.bleepingcomputer.com/news/s ... aster-key/
And a link to their forum topic: https://www.bleepingcomputer.com/forums ... extension/
And a link to their forum topic: https://www.bleepingcomputer.com/forums ... extension/
-
brycem
- New here
- Posts: 9
- Joined: Fri Oct 08, 2021 7:08 pm
Re: [RANSOMWARE] Deadbolt
A little bit of harmless hyperbole to emphasize the level of rage and contempt I feel for malware authors
No argument here from me. Sound points, one and all!The blame for this lies squarely on QNAP though. QNAP has repeatedly been exploited for more than six years now, and repeatedly by the same types of attack vector. Yet, during the past six years QNAP has done little to actually deal with and address the problem of the extremely poor coding practices (hard coded credentials in 2021? Seriously, wtf?) employed in the QTS operating environment and all the various "Q" applications.
QNAP has utterly decimated the basic security model of Linux and makes it all but impossible for any user to employ any of the basic security functions that are part of Linux. 3rd party application developers such as Plex have made requests to QNAP several years ago asking QNAP to at least make it possible for applications to run in their own user space and not be required run as Admin, for example. QNAP essentially told 3rd party application developers that were asking for better security models to take a long walk off of a short pier.
Instead, QNAP continued to muddy the already very muddy security waters by releasing QuFirewall and giving the impression that using QuFirewall made the NAS secure and could be made accessible from the Internet. Further muddying of the waters continued with never ending messaging and push to use Security Counselor, Maleware Remover, QVPN, automatic updates, etc. None of these action actually dealt with impeding attacks such as this and previous ransomware attacks.
QNAP has done absolutely nothing to impede the exploitation of these types of security vulnerabilities and has set-up their technology-illeterate and security-illiterate user base to be exploited by the plethora of security vulnerabilities that are present in the QTS operating environment and the "Q" applications.
With the release of the TS-509 Pro and all subsequent Intel x86 & x86_64 based NASes, there was no reason to keep QTS based on a crippled low powered embedded Linux type of build. The Linux build on home routers in many cases, are more robust and secure than the Linux build that QTS is based on.
On the Security>Convenience spectrum, I ran my QNAP in an entirely air-gapped environment (strictly USB in/out) for the last year... Having replaced my QTS and QuTS with TrueNAS recently, I've relaxed that security posture to expose Samba on a VLAN to select devices on my network, but I'm still a long way from UPnPAt this point? That is something that QNAP should have been actively advocating as far back as 2015.Disable port-forwards and UPnP should be considered a bare minimum at this point.
- Moogle Stiltzkin
- Guru
- Posts: 11448
- Joined: Thu Dec 04, 2008 12:21 am
- Location: Around the world....
- Contact:
Re: [RANSOMWARE] Deadbolt
yes, disable myqnapcloud, upnp, don' port forward your qnap stuff (like the qts admin port, the qts webservers...)okenny wrote: ↑Wed Jan 26, 2022 7:58 am What is the consensus.....Is it good enough to disable port forwarding, disable qnap cloud and disable upnp?
Do I need to place the NAS on a VLAN without any WAN access too? I was hesitant to do this, as it's a pain in the a to run the NAS on a separate VLAN.
I am going to start building a freenas server I think, I'm sick of this.
from what i hear, plex port forward might be ok.
https://www.reddit.com/r/PleX/comments/ ... _qnap_nas/
https://www.reddit.com/r/qnap/comments/ ... _for_plex/
VPN might be ok as well (assuming your vpn server is either a raspberrypi or better yet your router like a pfsense)
If you need remote, i particularly like lawrençe's setup for this (my preference is using pfsense and managed switches though). In his setup he has 2 different nas for 2 different purposes. One is used for remote, and the other is strictly for local. And he segregrates them out so the one at risk is not gonna mess up the other devices on the private lan if a breach does happen.
https://youtu.be/A1I1k9Nct-A?t=158
Tutorial: pfsense OpenVPN Configuration For Remote Users 2020
https://youtu.be/PgielyUFGeQ
Creating a WireGuard VPN Server on RaspberryPi - 4K TUTORIAL
https://youtu.be/lnYYmC-A4S0?t=497
this is how i imagine the vpn should be used as for remote roughly (ideally the vpn server is run on the router using either openvpn or wireguard, not the nas e.g. qvpn
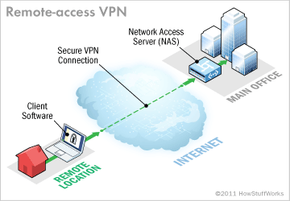
https://computer.howstuffworks.com/vpn.htm
dyor
https://www.reddit.com/r/synology/comme ... use_which/
https://www.reddit.com/r/HomeNetworking ... ss_my_nas/
https://www.reddit.com/r/synology/comme ... _nas_from/
that said, my setup is strictly lan only, so i never have to worry about qlocker or these kind of things. I make sure i update my router, my qnap nases, my client devices ( os and apps. for desktops i use KCS SUMo to figure out whats outdated that needs updating https://www.kcsoftwares.com/sumo/start/ ), don't visit dodgy sites, don't download pirated stuff, set your windows desktop to a non admin account. And run your backup jobs from time to time. Haven't had a problem following these golden rules :/
Last edited by Moogle Stiltzkin on Wed Jan 26, 2022 11:50 am, edited 6 times in total.
NAS
[Main Server] QNAP TS-877 (QTS) w. 4tb [ 3x HGST Deskstar NAS & 1x WD RED NAS ] EXT4 Raid5 & 2 x m.2 SATA Samsung 850 Evo raid1 +16gb ddr4 Crucial+ QWA-AC2600 wireless+QXP PCIE
[Backup] QNAP TS-653A (Truenas Core) w. 4x 2TB Samsung F3 (HD203WI) RaidZ1 ZFS + 8gb ddr3 Crucial
[^] QNAP TL-D400S 2x 4TB WD Red Nas (WD40EFRX) 2x 4TB Seagate Ironwolf, Raid5
[^] QNAP TS-509 Pro w. 4x 1TB WD RE3 (WD1002FBYS) EXT4 Raid5
[^] QNAP TS-253D (Truenas Scale)
[Mobile NAS] TBS-453DX w. 2x Crucial MX500 500gb EXT4 raid1
Network
Qotom Pfsense|100mbps FTTH | Win11, Ryzen 5600X Desktop (1x2tb Crucial P50 Plus M.2 SSD, 1x 8tb seagate Ironwolf,1x 4tb HGST Ultrastar 7K4000)
Resources
[Review] Moogle's QNAP experience
[Review] Moogle's TS-877 review
https://www.patreon.com/mooglestiltzkin
[Main Server] QNAP TS-877 (QTS) w. 4tb [ 3x HGST Deskstar NAS & 1x WD RED NAS ] EXT4 Raid5 & 2 x m.2 SATA Samsung 850 Evo raid1 +16gb ddr4 Crucial+ QWA-AC2600 wireless+QXP PCIE
[Backup] QNAP TS-653A (Truenas Core) w. 4x 2TB Samsung F3 (HD203WI) RaidZ1 ZFS + 8gb ddr3 Crucial
[^] QNAP TL-D400S 2x 4TB WD Red Nas (WD40EFRX) 2x 4TB Seagate Ironwolf, Raid5
[^] QNAP TS-509 Pro w. 4x 1TB WD RE3 (WD1002FBYS) EXT4 Raid5
[^] QNAP TS-253D (Truenas Scale)
[Mobile NAS] TBS-453DX w. 2x Crucial MX500 500gb EXT4 raid1
Network
Qotom Pfsense|100mbps FTTH | Win11, Ryzen 5600X Desktop (1x2tb Crucial P50 Plus M.2 SSD, 1x 8tb seagate Ironwolf,1x 4tb HGST Ultrastar 7K4000)
Resources
[Review] Moogle's QNAP experience
[Review] Moogle's TS-877 review
https://www.patreon.com/mooglestiltzkin
- cs7404
- Know my way around
- Posts: 186
- Joined: Thu Jan 20, 2022 10:13 pm
Re: [RANSOMWARE] Deadbolt
well said ..Cbrad01 wrote: ↑Wed Jan 26, 2022 10:43 am People need to stop exposing their NASs to the internet and QNAP needs to ditch the current os and all of the ** applications that create so many holes by trying to be the easy, no fuse internet cloud.
Google, Apple, Amazon and so spend billions on their cloud options to keep them secure and rebuts yet QNAP marketing let’s folks think they can do the same for a few hundred bucks and this is where we are.
QNAP has created a insecure OS with their decisions over time to make things easy and then putting crappy apps on top that all run privileged because it’s easy.
But with that said I am surprised that anyone thinks it’s safe to share their devices on the internet(regardless of what device it is).
Unless you are prepared to spend the time and resources to protect yourself leave cloud sharing to the big boys and use their services. Use your NAS inside your network to to share…
Sent from my iPad using Tapatalk
been using NAS for years - restricted to LAN access only - to avoid phone home phenomena that can be exploited. not too long ago WD's My Cloud was targeted and the exploit was able to remotely erase devices .. express lane into the NAS OS using the phone home link established with their maker.
after moving into the QNAP space and seeing the large amount of connected apps available on QTS, I blocked internet access at the router level.
never did trust the 'connected' life, especially with my data ..
if i want access to my NAS from the outside world i rely on my router's VPN server.
----------
TS-453D
QTS 5.1.1.2491
TS-453D
QTS 5.1.1.2491
-
citgtech
- First post
- Posts: 1
- Joined: Wed Jan 26, 2022 11:43 am
Re: [RANSOMWARE] Deadbolt
We paid the ransom for a client and it didn't work!!
My thought is that the instructions say to send .030000 (exactly). I copied and pasted that in Coinbase, but once the transaction has settled it now shows .03000165 instead. I don't know how picky it is since they actually get MORE $, but that's the only reason I can see for it to not have worked. I see the OP_RETURN output as the instructions say, but when I copy/paste the decryption key to the NAS page it just says "invalid decryption key entered"
I guess now we wait for QNAP to do the right thing!
My thought is that the instructions say to send .030000 (exactly). I copied and pasted that in Coinbase, but once the transaction has settled it now shows .03000165 instead. I don't know how picky it is since they actually get MORE $, but that's the only reason I can see for it to not have worked. I see the OP_RETURN output as the instructions say, but when I copy/paste the decryption key to the NAS page it just says "invalid decryption key entered"
I guess now we wait for QNAP to do the right thing!
-
mikaux
- New here
- Posts: 9
- Joined: Mon Jul 13, 2015 6:16 am
Re: Deadbolt ransomware
Can you provide a more detailed explanation of how to do this. I can get in via SSH but dont know where to go from there.skaox wrote: ↑Wed Jan 26, 2022 7:49 am I don't know why but the little b@stard didn't had time to crypt anything.
If you want to have access to your NAS just connect to ssh with admin account (or root if you have Entware-alt installed and admin disabled) :
cd /home/httpd/
mv index.html index.html_deadlock
mv index.html.bak index.html
Now you can access again to the administration panel
The index.html start like that :
#!/bin/sh
echo "Content-Type: text/html"
echo ""
get_value () {
echo "$1" | awk -F "${2}=" '{ print $2 }' | awk -F '&' '{ print $1 }'
}
not_running() { echo '{"status":"not_running"}'; exit; }
PID_FILENAME=/tmp/deadbolt.pid
STATUS_FILENAME=/tmp/deadbolt.status
FINISH_FILENAME=/tmp/deadbolt.finish
TOOL=/mnt/HDA_ROOT/27855
CRYPTDIR=/share
In process list you should have a few (5-6) process related to /mnt/HDA_ROOT/27855 -> kill them
I've launched a scan with Malware Remover but nothing was found.
I didn't reboot the NAS for the moment and I'm searching if there is more.
When opening QuLog Center you will have a message :
You must configure the destination volume for storing logs before enabling this feature.
Go to Log Settings to configure the destination volume of the event logs.
In Log Settings, Event and Access Log Destination will be empty.
I can't rename, delete or move 27855 (ELF packed with UPX) and nothing in /etc/config/crontab.
To be continue
-
skaox
- New here
- Posts: 6
- Joined: Sat Oct 31, 2020 4:02 am
Re: [RANSOMWARE] Deadbolt
cd /home/httpd/
mv index.html index.html_deadlock
mv index.html.bak index.html
BUT it will come back after reboot.
mv index.html index.html_deadlock
mv index.html.bak index.html
BUT it will come back after reboot.
Last edited by skaox on Wed Jan 26, 2022 12:17 pm, edited 1 time in total.
- OneCD
- Guru
- Posts: 12144
- Joined: Sun Aug 21, 2016 10:48 am
- Location: "... there, behind that sofa!"
Re: [RANSOMWARE] Deadbolt
You may need to first exit from the console menu if it's enabled in your firmware.
-
nonojapan
- Starting out
- Posts: 17
- Joined: Wed Jan 26, 2022 12:14 pm
Re: [RANSOMWARE] Deadbolt
Any one have a tutorial how to login on the infected Deadbolt NAS and bypass the ransomware message? Any tutorial from qnap on how to remove it?
-
skaox
- New here
- Posts: 6
- Joined: Sat Oct 31, 2020 4:02 am
Re: Deadbolt ransomware
Yes I confirm having SDDPd.bin who's responsible for creating the index.html and there is also a .SDDPd_required but mine is empty.pofjybkh wrote: ↑Wed Jan 26, 2022 8:05 am
Mine was called 31888 (so the name is random), but I compared the content of mine with yours and they are identical.
Also, if it helps with your investigation, the initial payload seems to come from /mnt/HDA_ROOT/update_pkg/SDDPd.bin (this name might also be random), which writes the index.html, but neither of them actually starts the encryption process, so that's still unclear.
I powered-off mine as soon as I noticed, so I only lost a few files, but this way I lost the option of doing the 7z log trick.
I'll power it on again tomorrow with only one of the disks in and maybe the process will start again...
I've searched for the .deadbolt files :
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/client/20210702_183205/qsync.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/client/20210706_093435/qsync.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/client/20210722_123031/qsync.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/client/20210724_162013/qsync.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/client/20210730_215512/qsync.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/client/20210730_223857/qsync.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/client/20210730_232622/qsync.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/client/20210810_023638/qsync.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/client/20210810_210501/qsync.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/client/20210811_140010/qsync.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/client/20210813_013819/qsync.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/client/20211007_151948/qsync.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/client/20211014_091217/qsync.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/client/20211021_211401/qsync.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/client/20211021_213922/qsync.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/client/20211021_221457/qsync.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/client/20211022_050147/qsync.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/client/20211109_102353/qsync.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/rtrrs/20211014_091217/qsyncd.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/rtrrs/20211021_211401/qsyncd.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/rtrrs/20211021_213922/qsyncd.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/rtrrs/20211021_221457/qsyncd.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/rtrrs/20211022_050147/qsyncd.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/rtrrs/20211109_102353/qsyncd.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/rr2s/20211014_091217/rr2_server.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/rr2s/20211014_091217/service_gateway.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/rr2s/20211021_211401/rr2_server.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/rr2s/20211021_211401/service_gateway.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/rr2s/20211021_213922/rr2_server.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/rr2s/20211021_213922/service_gateway.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/rr2s/20211021_221457/rr2_server.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/rr2s/20211021_221457/service_gateway.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/rr2s/20211022_050147/rr2_server.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/rr2s/20211022_050147/service_gateway.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/rr2s/20211109_102353/rr2_server.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/rr2s/20211109_102353/service_gateway.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/latest_backup/service_gateway.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/latest_backup/rr2_server.conf.deadbolt
/share/CACHEDEV1_DATA/.@qsync/detail-logs/hbs_bak/latest_backup/qsyncd.conf.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/db.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/servers.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/user.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/proc.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/help_topic.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/proxies_priv.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/time_zone_name.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/plugin.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/event.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/func.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/columns_priv.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/general_log.CSV.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/help_keyword.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/host.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/ndb_binlog_index.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/help_category.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/procs_priv.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/help_relation.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/slow_log.CSV.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/tables_priv.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/time_zone.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/time_zone_leap_second.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/time_zone_transition.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/mysql/time_zone_transition_type.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/songTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/videoAlbumTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/objDeletionTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/pictureKeyWordMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/ExSongTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/KTVArtistMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/KTVArtistSearchPattern.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/MusicVideoAlbumTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/MusicVideoArtistTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/StorageTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/appTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/albumTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/artistTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/faceClusterTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/faceGroupArchive.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/pictureFaceNameTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/pictureImgClass.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/pictureImgClassError.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/videoTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/videoMyFavorite.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/ACL2Table.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/faceFeatureTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/ACLTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/ACL3Table.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/KTVGenreMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/KTVLyricsMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/dirTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/pictureFaceTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/pictureKeyWordTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/placeAddressUnit.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/placeAddress.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/playlistTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/songKeyWordMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/playmediaTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/videoDirectorTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/videoGenreMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/TrashBin.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/videoActorTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/pictureImgHash.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/systemTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/TVShowEpisode.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/faceGroupTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/faceTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/pictureAlbumTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/songKeyWordTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/KTVTitleSearchPattern.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/faceClusterSuggestion.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/faceGroupArchivePictureMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/faceGroupClusterSummary.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/favoriteContent.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/genreTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/pictureMyFavorite.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/pictureTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/playHistoryTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/videoDirectorMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/videoGenreTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/subtypeTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/faceGroupClusterMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/pictureAlbumMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/pictureFaceNameSuggestionTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/KTVGenreTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/pictureImgClassMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/KTVArtistTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/MusicVideoGenreTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/pictureImgClassSynonym.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/songMyFavorite.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/videoActorMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s00/videoAlbumMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/StorageTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/systemTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/appTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/TrashBin.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/songTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/videoAlbumTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/videoGenreTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/ExSongTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/KTVArtistMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/KTVArtistSearchPattern.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/MusicVideoAlbumTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/MusicVideoArtistTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/faceClusterTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/faceGroupArchive.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/faceGroupArchivePictureMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/albumTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/objDeletionTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/artistTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/pictureFaceNameTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/pictureImgClass.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/pictureImgClassError.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/pictureAlbumTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/pictureKeyWordMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/playHistoryTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/videoTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/pictureKeyWordTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/dirTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/KTVArtistTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/pictureImgClassMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/KTVGenreTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/pictureImgClassSynonym.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/videoDirectorTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/videoGenreMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/songMyFavorite.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/songKeyWordMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/placeAddress.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/faceFeatureTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/ACL3Table.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/KTVLyricsMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/MusicVideoGenreTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/ACLTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/ACL2Table.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/faceGroupClusterMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/pictureFaceNameSuggestionTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/pictureAlbumMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/placeAddressUnit.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/playlistTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/videoActorMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/videoAlbumMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/videoMyFavorite.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/videoActorTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/pictureFaceTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/TVShowEpisode.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/faceClusterSuggestion.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/faceGroupClusterSummary.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/genreTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/faceGroupTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/KTVGenreMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/KTVTitleSearchPattern.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/faceTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/favoriteContent.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/pictureImgHash.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/pictureMyFavorite.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/playmediaTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/songKeyWordTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/subtypeTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/videoDirectorMapping.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/data/s01/pictureTable.MYD.deadbolt
/share/CACHEDEV1_DATA/.system/kmsg_backup.1.gz.deadbolt
/share/CACHEDEV1_DATA/.system/music/dan o@27connor @28danosongs.com@29/sample music 3.jpg.deadbolt
/share/CACHEDEV1_DATA/.system/music/dan o@27connor @28danosongs.com@29/sample music 3-1.jpg.deadbolt
/share/CACHEDEV1_DATA/.system/music/dan o@27connor @28danosongs.com@29/sample music 5-1.jpg.deadbolt
/share/CACHEDEV1_DATA/.system/music/dan o@27connor @28danosongs.com@29/sample music 5.jpg.deadbolt
/share/CACHEDEV1_DATA/.system/music/UNKNOWN/israel kamakawiwo@27ole - somewhere over the rainbow @28with@29-1.jpg.deadbolt
/share/CACHEDEV1_DATA/.system/music/UNKNOWN/israel kamakawiwo@27ole - somewhere over the rainbow @28with@29.jpg.deadbolt
/share/CACHEDEV1_DATA/.system/thumbnail/10a/510730.jpg.deadbolt
/share/CACHEDEV1_DATA/.system/thumbnail/10a/510730-1.jpg.deadbolt
/share/CACHEDEV1_DATA/.system/thumbnail/10a/510730-2.jpg.deadbolt
...
167867 /share/CACHEDEV1_DATA/.system/thumbnail/...
...
/share/CACHEDEV1_DATA/.system/thumbnail/10b/510475-2.jpg.deadbolt
/share/CACHEDEV1_DATA/.system/s00_20210702_215932.sql.deadbolt
/share/CACHEDEV1_DATA/.system/s01_20210702_182606.sql.deadbolt
/share/CACHEDEV1_DATA/.system/log/mymedia_cli.log.4.gz.deadbolt
/share/CACHEDEV1_DATA/.system/log/mymedia_cli.log.5.gz.deadbolt
/share/CACHEDEV1_DATA/.system/log/mymedia_cli.log.1.gz.deadbolt
/share/CACHEDEV1_DATA/.system/log/mymedia_cli.log.2.gz.deadbolt
/share/CACHEDEV1_DATA/.system/log/myidbserver.log.2.gz.deadbolt
/share/CACHEDEV1_DATA/.system/log/myidbserver.log.3.gz.deadbolt
/share/CACHEDEV1_DATA/.system/log/myidbserver.log.1.gz.deadbolt
/share/CACHEDEV1_DATA/.system/log/myidbserver.log.4.gz.deadbolt
/share/CACHEDEV1_DATA/.system/log/mymedia_cli.log.3.gz.deadbolt
/share/CACHEDEV1_DATA/.system/XcodeFile.db.deadbolt
/share/CACHEDEV1_DATA/.system/MyTranscodeDB.bak.deadbolt
/share/CACHEDEV1_DATA/.system/idbserver.conf.deadbolt
/share/CACHEDEV1_DATA/.system/s00_20201125_201620.sql.deadbolt
/share/CACHEDEV1_DATA/.system/s00_20201125_201931.sql.deadbolt
/share/CACHEDEV1_DATA/.system/s00_20201125_201923.sql.deadbolt
-
mikaux
- New here
- Posts: 9
- Joined: Mon Jul 13, 2015 6:16 am
Re: [RANSOMWARE] Deadbolt
I am able to access the NAS through the QFinder app, sometimes I get the DEADBOLT Splash Page, but delete the extra code in the address line and it goes away.
The Deadbolt has attached some Vols and not others on my NAS. So, some data is totally locked away by Deadbolt, but other whole swathes of data and multimedia is untouched. Not sure if its about to launch against those not yet infected and am really hopeing someone has an idiots guide to finding this thing and deleting it. I am resigned to having to restore those files it has killed alread, luckily I have a cloud backup of all files.
Any advice appreciated. I dont know how to search for the DEADBOLT files on the NAS - thats my main issue.
The Deadbolt has attached some Vols and not others on my NAS. So, some data is totally locked away by Deadbolt, but other whole swathes of data and multimedia is untouched. Not sure if its about to launch against those not yet infected and am really hopeing someone has an idiots guide to finding this thing and deleting it. I am resigned to having to restore those files it has killed alread, luckily I have a cloud backup of all files.
Any advice appreciated. I dont know how to search for the DEADBOLT files on the NAS - thats my main issue.
Last edited by mikaux on Wed Jan 26, 2022 1:51 pm, edited 1 time in total.
-
Ramias
- New here
- Posts: 9
- Joined: Wed Oct 26, 2016 8:33 am
Re: [RANSOMWARE] Deadbolt
For those attacked by this: was your NAS on the internet or did you have UPNP enabled or were you using MyQnapCloud?

















